IT Security Report Template: How to Create an Effective and Comprehensive Security Report
Learn how to create an effective IT Security Report using our template. Our step-by-step guide will help you create a comprehensive report that covers all aspects of your organization’s security.
In today’s digital age, ensuring the security of your organization’s data and systems is more critical than ever. With the increasing frequency and sophistication of cyber attacks, IT security teams need to have a clear understanding of their organization’s security posture and be able to communicate it effectively to stakeholders.
Creating an IT Security Report can be a daunting task, but with our template and step-by-step guide, you can create an effective and comprehensive report that covers all aspects of your organization’s security. Here’s how to get started:
Step 1: Define the Scope of the Report
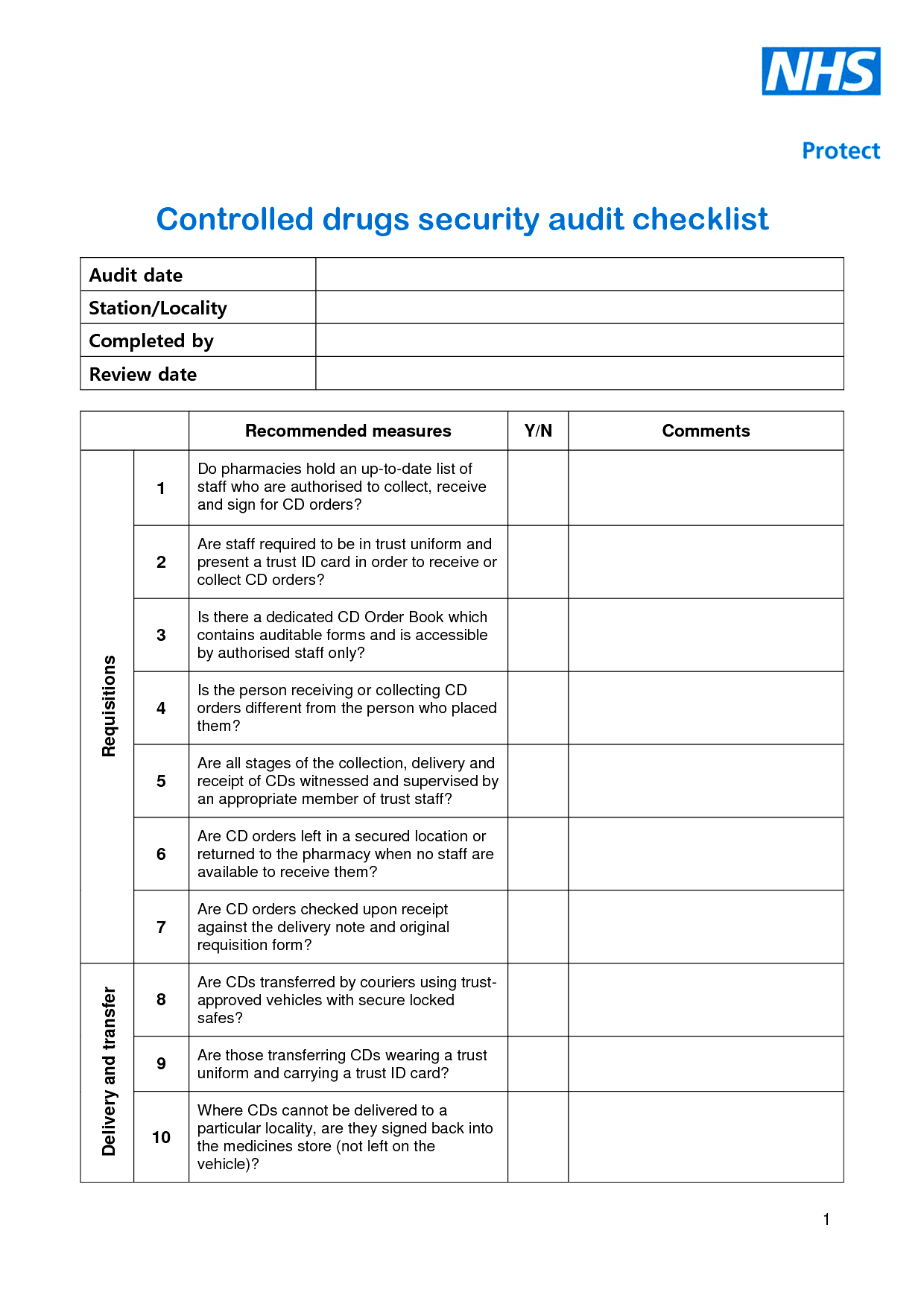
The first step in creating an IT Security Report is to define the scope of the report. This includes identifying the areas of your organization that you will be reporting on, such as network security, application security, data security, and physical security. You should also define the timeframe that the report will cover, such as the past quarter or year.
Step 2: Collect and Analyze Data
The next step is to collect and analyze data related to the areas identified in step 1. This may include data from security tools such as firewalls and intrusion detection systems, vulnerability scans, and user activity logs. You should also gather information from stakeholders, such as employees and third-party vendors.
Once you have collected the data, analyze it to identify any trends or patterns that may indicate a security issue. This will help you to prioritize areas that require immediate attention and create a more effective report.
Step 3: Create the Report
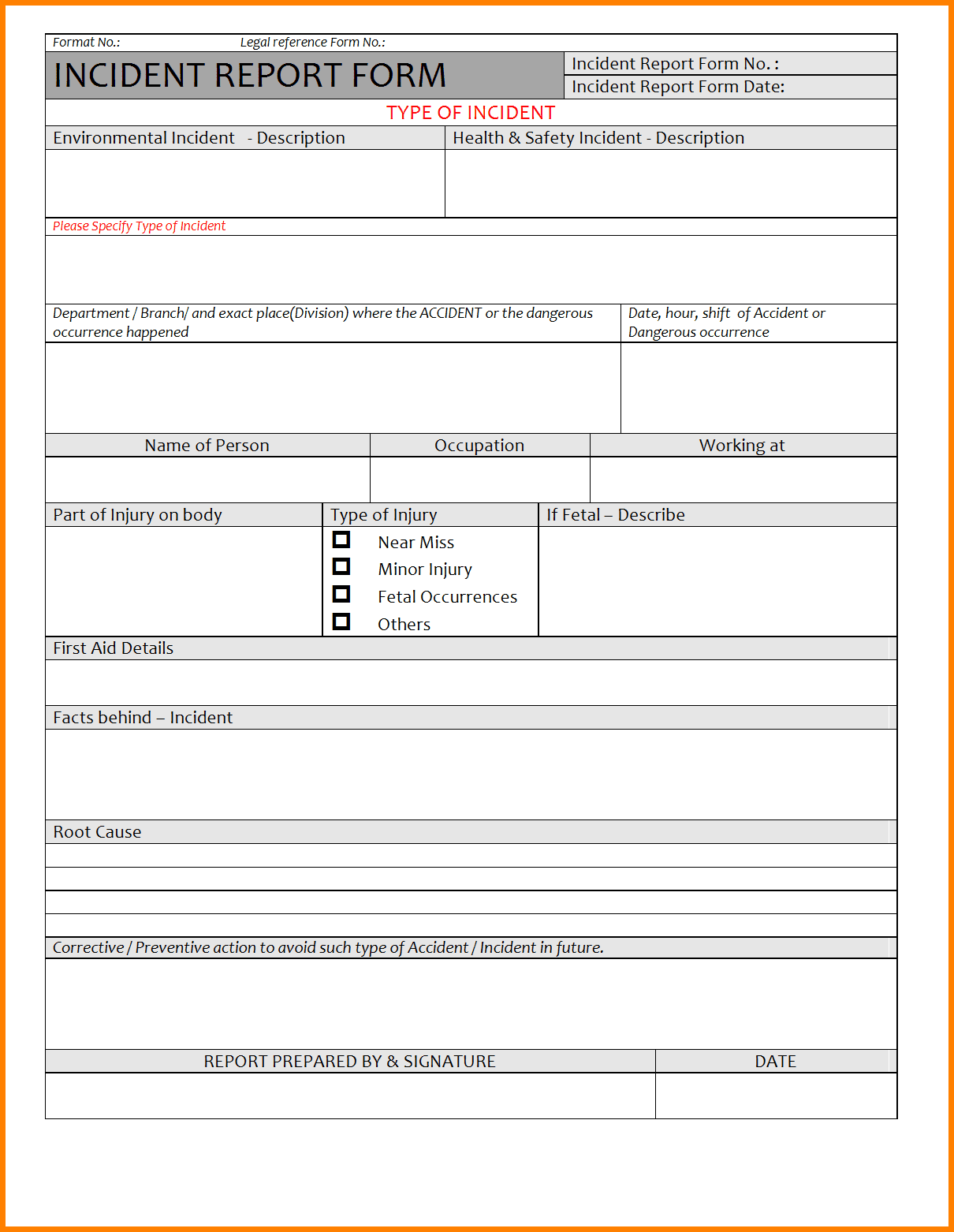
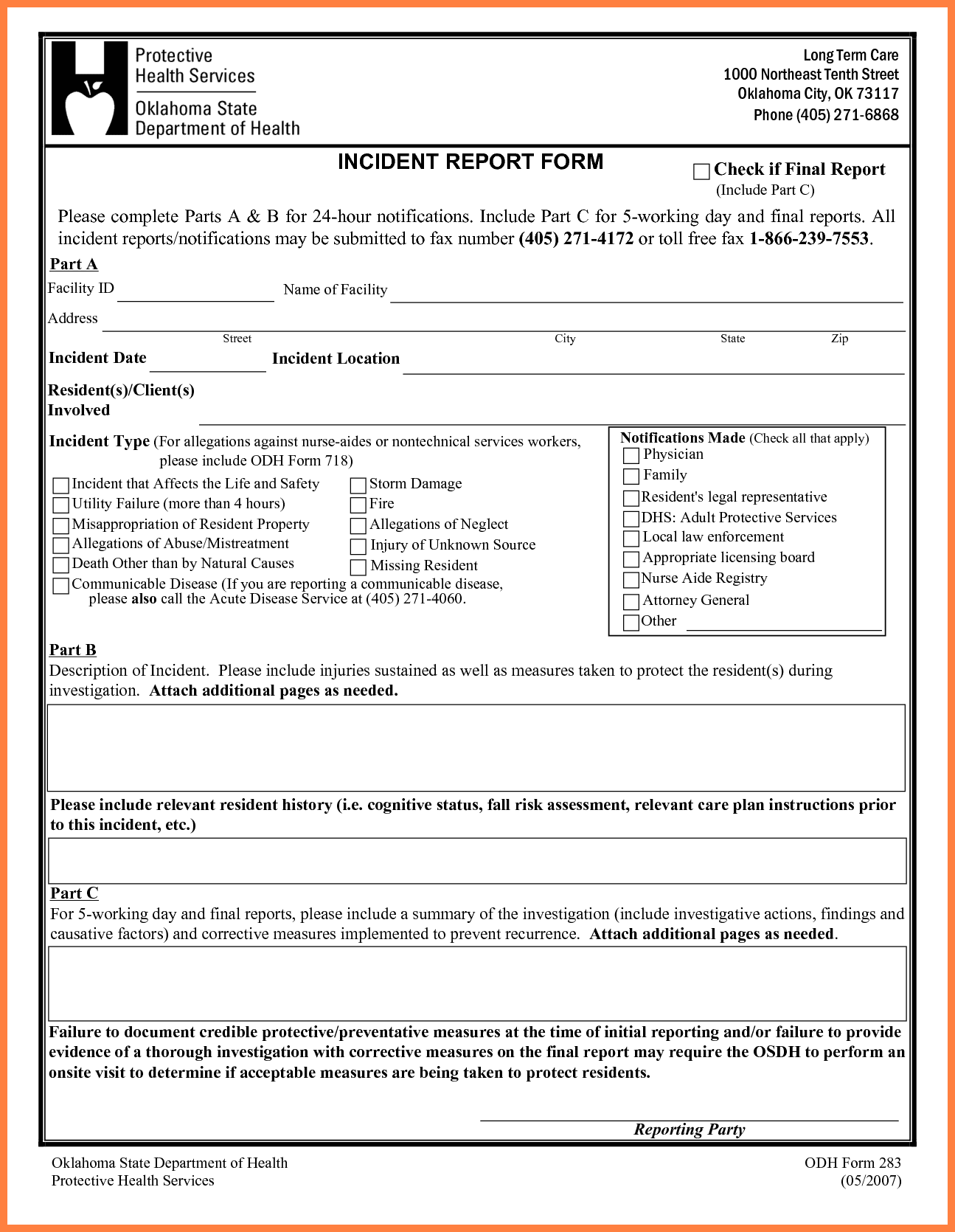
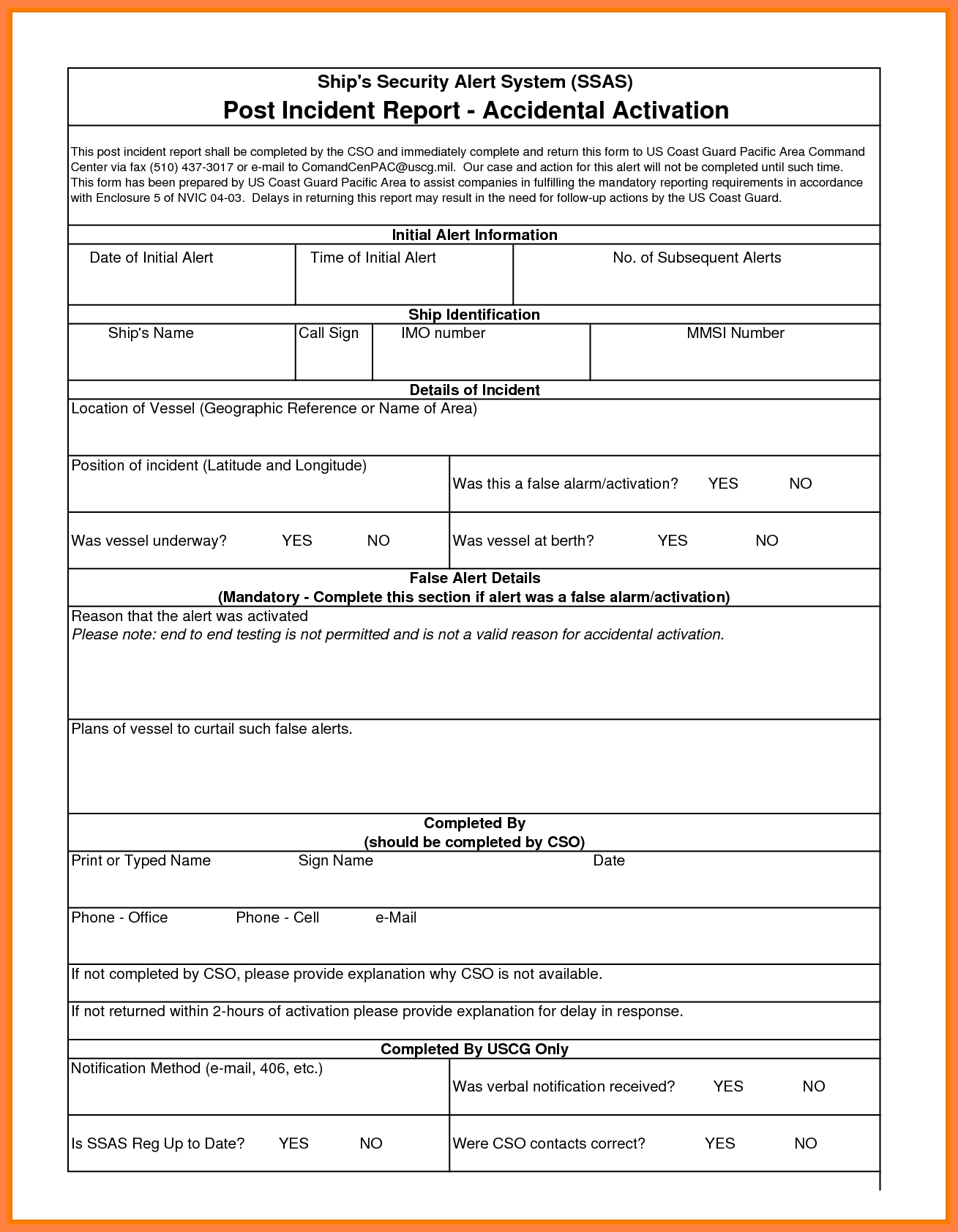
Using our IT Security Report Template, you can create a comprehensive report that covers all aspects of your organization’s security. The template includes sections for network security, application security, data security, and physical security, as well as an executive summary and recommendations for improvement.
When creating the report, be sure to include both quantitative and qualitative data, as well as any relevant charts and graphs that help to illustrate key findings. The report should be easy to read and understand for both technical and non-technical stakeholders.
Step 4: Review and Share the Report
Before sharing the report, be sure to review it carefully to ensure that it is accurate and complete. You should also seek feedback from stakeholders to ensure that the report meets their needs and addresses any concerns they may have.
Once you have finalized the report, share it with stakeholders, such as executives, board members, and IT staff. This will help to ensure that everyone in your organization is aware of the current security posture and understands the steps that are being taken to improve it.
Conclusion
Creating an IT Security Report can be a challenging task, but with our template and step-by-step guide, you can create a comprehensive and effective report that covers all aspects of your organization’s security. By following these steps, you can ensure that your organization is prepared to defend against the ever-evolving threat of cyber attacks.
In addition to the steps outlined above, there are a few best practices that you should keep in mind when creating an IT Security Report. These include:
- Use a clear and concise writing style. Avoid technical jargon and acronyms that may be unfamiliar to stakeholders.
- Include an executive summary at the beginning of the report. This should provide a high-level overview of the report’s key findings and recommendations.
- Use visuals such as charts, graphs, and tables to help illustrate key findings. This can make the report easier to understand for non-technical stakeholders.
- Consider using a risk-based approach to prioritize areas that require immediate attention. This can help to ensure that limited resources are focused on the areas of greatest risk.
- Be sure to include recommendations for improvement based on your findings. This can help to ensure that your organization is continuously improving its security posture.
By following these best practices, you can create an IT Security Report that is not only informative but also actionable. This can help your organization to better understand its security posture and take steps to improve it.
At Pruneyardinn.com, we understand the importance of IT security and the challenges that organizations face in ensuring the security of their data and systems. That’s why we’ve developed an IT Security Report Template that is designed to help organizations create effective and comprehensive security reports.
Our template includes all the sections that you need to create a comprehensive IT Security Report, including network security, application security, data security, and physical security. We’ve also included an executive summary and recommendations for improvement, as well as tips and best practices for creating an effective report.
Whether you’re a small business or a large enterprise, our IT Security Report Template can help you to better understand your organization’s security posture and take steps to improve it. So why wait? Download our template today and start creating an effective and comprehensive IT Security Report for your organization.