How to Create an Effective Security Report Example
Learn how to create an effective security report example to ensure the safety and security of your business or organization. Our guide will provide you with tips and best practices for creating a comprehensive security report that can help you prevent and respond to security threats.
Security is a critical aspect of any business or organization. Without proper security measures in place, your business may be vulnerable to a wide range of threats, from theft and vandalism to cyber attacks and terrorism. To ensure the safety and security of your business or organization, it is essential to have an effective security report in place.
In this article, we will guide you through the process of creating an effective security report example. We will provide you with tips and best practices for creating a comprehensive security report that can help you prevent and respond to security threats.
Identify the Purpose and Scope of the Report
The first step in creating an effective security report example is to identify the purpose and scope of the report. The purpose of the report should be clear and concise, and it should outline the key objectives and goals of the report. The scope of the report should also be defined, including the areas that will be covered, the timeframe of the report, and the intended audience.
Collect Relevant Data and Information
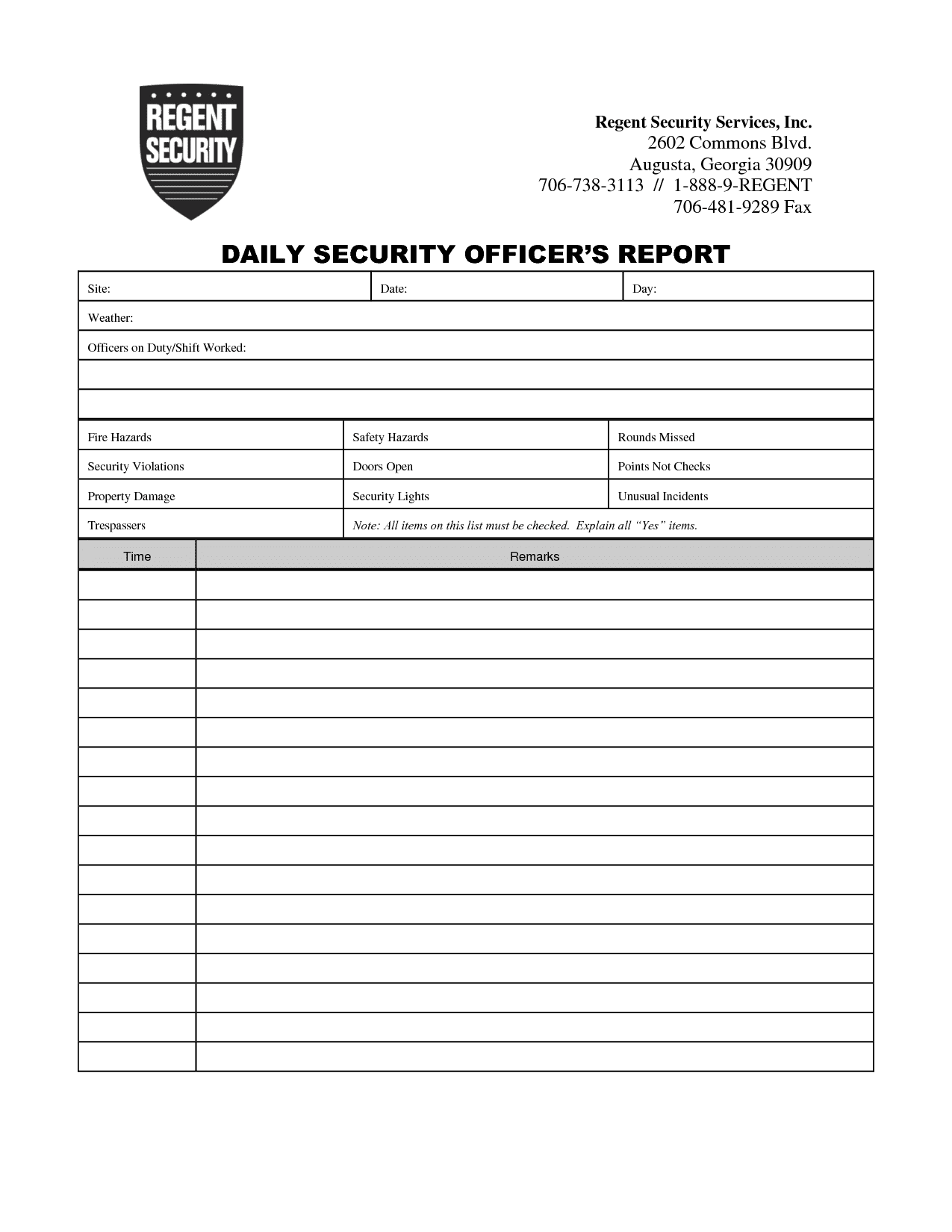
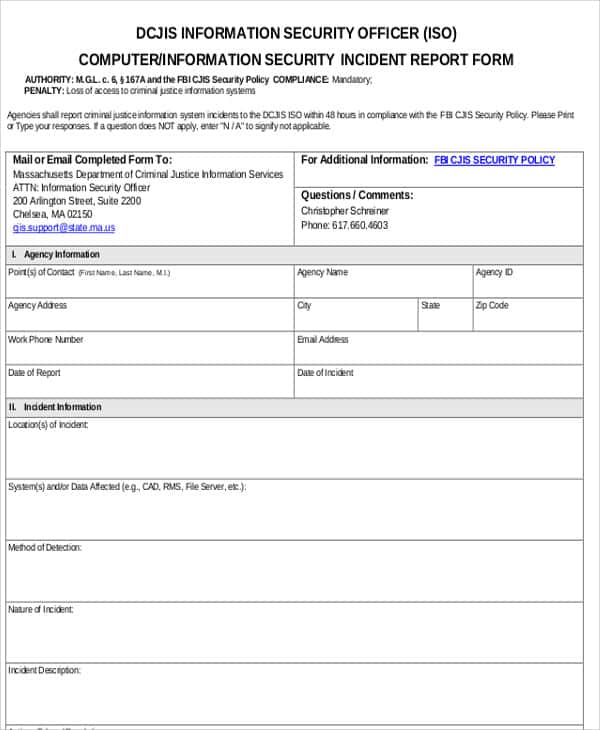
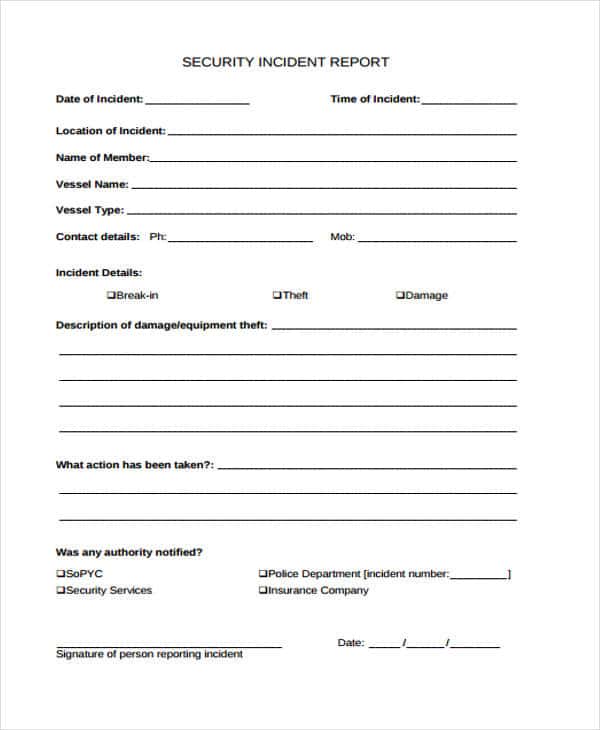
Once you have identified the purpose and scope of the report, the next step is to collect relevant data and information. This may include incident reports, security logs, surveillance footage, and other relevant information. It is important to ensure that the information you collect is accurate, relevant, and reliable.
Analyze the Data and Information
After collecting the relevant data and information, the next step is to analyze it. This involves identifying patterns, trends, and anomalies in the data that may indicate potential security threats. It is important to use a systematic approach to analyzing the data, such as the SARA (Scanning, Analysis, Response, Assessment) model.
Develop Recommendations and Action Plans
Based on the analysis of the data, the next step is to develop recommendations and action plans. These may include new security policies and procedures, training and education programs for staff, improvements to physical security measures, and the implementation of new security technologies.
Present the Findings and Recommendations
The final step in creating an effective security report example is to present the findings and recommendations. This may include a written report, a presentation, or both. It is important to ensure that the report is clear, concise, and easy to understand, and that it includes all relevant information and data.
Additionally, it is important to regularly review and update your security report to ensure that it remains effective and relevant. Threats and risks can evolve over time, and your security measures should evolve with them.
When presenting your security report, it is important to communicate the information clearly and effectively. Make sure to use language that is easy to understand, and avoid technical jargon unless it is necessary. Use graphs, charts, and other visual aids to help illustrate your points and make the information easier to digest.
It is also important to consider the audience when presenting your security report. Different audiences may have different needs and interests, and you should tailor your report accordingly. For example, senior executives may be more interested in high-level overviews and recommendations, while security personnel may be more interested in detailed incident reports and analysis.
Finally, make sure to follow up on the recommendations and action plans outlined in your security report. Review progress regularly and make adjustments as necessary. Keep track of any incidents or security breaches that occur and use them as opportunities to refine and improve your security measures.
In conclusion, creating an effective security report example is an important part of ensuring the safety and security of your business or organization. By following the steps outlined in this article and regularly reviewing and updating your security report, you can stay one step ahead of potential security threats and keep your business or organization safe and secure.