Learn about the different types of incident reports and get access to samples of incident report templates to ensure accurate and complete reporting.
Incident reports are an essential part of any organization’s risk management process. They provide a detailed account of any unusual events or accidents that occur in the workplace, helping organizations identify and mitigate potential hazards. However, writing an incident report can be a daunting task, particularly if you’ve never done it before. In this article, we’ll explore the different types of incident reports and provide you with samples of incident report templates to make reporting easier.
Types of Incident Reports
There are several different types of incident reports, each of which serves a specific purpose. Here are some of the most common types of incident reports:
- Workplace Injury or Illness Report
This type of report is used to document any injuries or illnesses that occur in the workplace. It’s important to report any incidents promptly to ensure that the injured party receives appropriate medical care. - Property Damage Report
This report is used to document any damage that occurs to company property, such as equipment or vehicles. Accurately documenting damage is crucial for insurance purposes and to prevent further damage to company property. - Near Miss Report
A near miss is an incident that could have resulted in injury or property damage but did not. Reporting near misses can help identify potential hazards and prevent future incidents. - Security Incident Report
This report is used to document any security-related incidents, such as theft or vandalism. Accurate reporting is essential for identifying patterns and preventing future security breaches.
Samples of Incident Report Templates
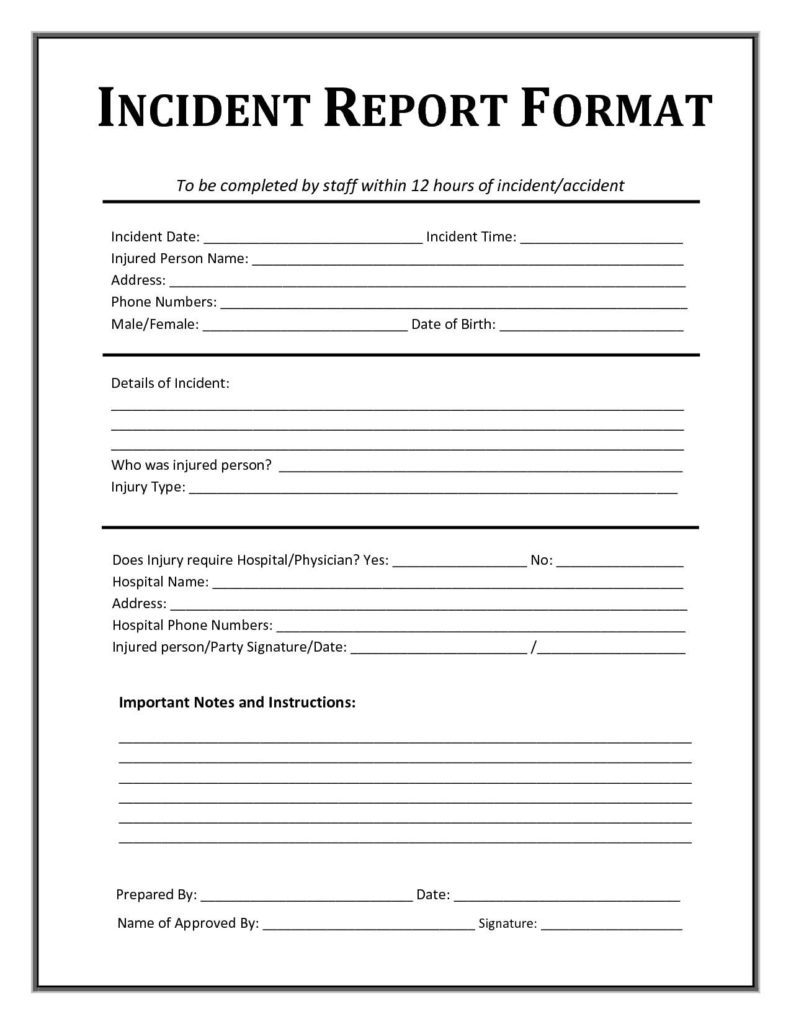
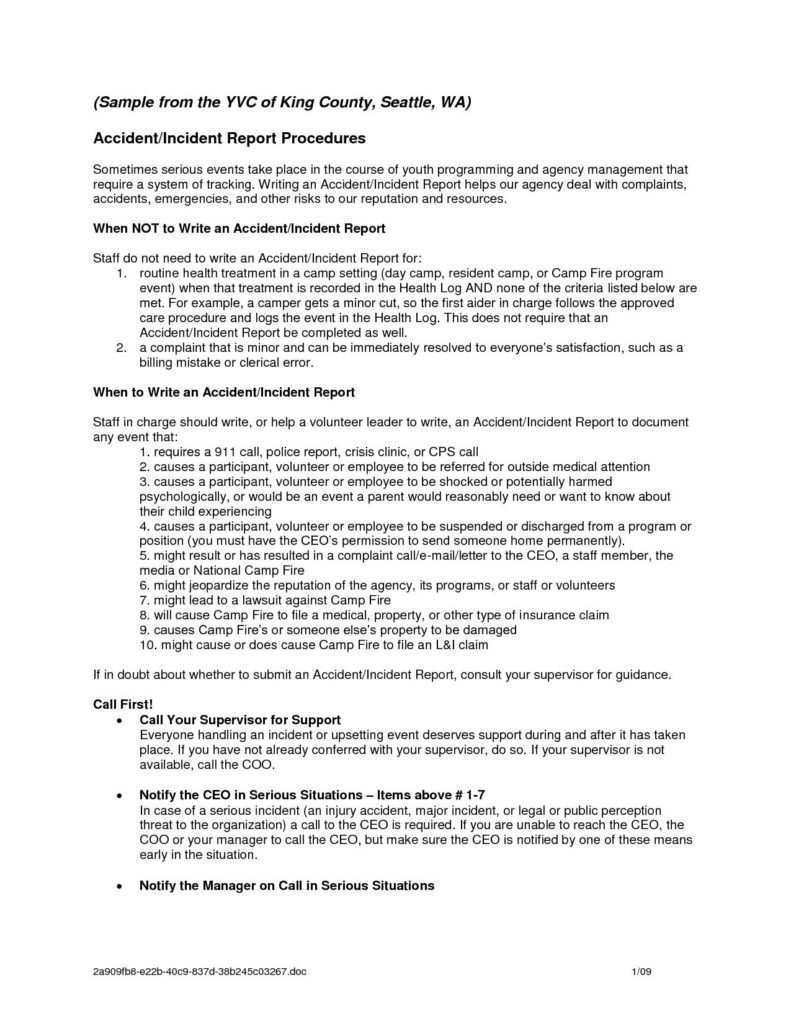
To make incident reporting easier, we’ve provided samples of incident report templates that you can use as a starting point. These templates can be customized to fit the specific needs of your organization.
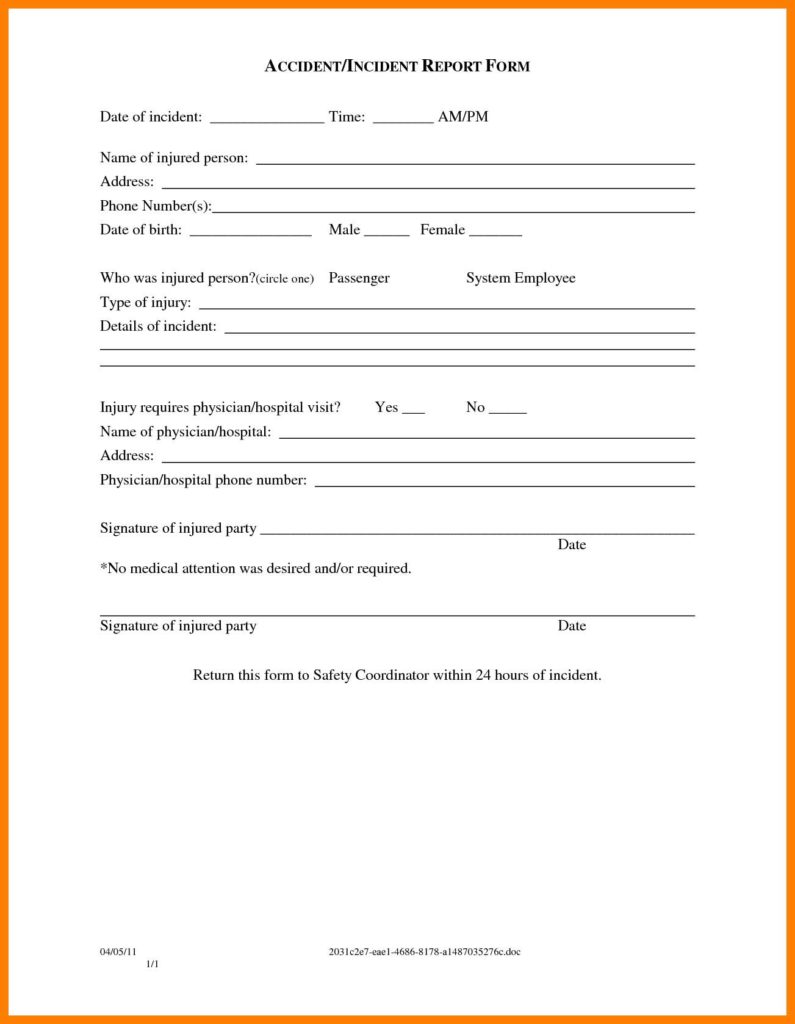
- Workplace Injury or Illness Report Template
This template includes fields for documenting the date, time, location, and details of the injury or illness. It also includes sections for witness statements and a summary of medical treatment. - Property Damage Report Template
This template includes fields for documenting the date, time, location, and details of the damage. It also includes sections for photographs of the damage and a summary of repairs needed. - Near Miss Report Template
This template includes fields for documenting the date, time, location, and details of the near miss. It also includes sections for identifying potential hazards and recommendations for preventing future incidents. - Security Incident Report Template
This template includes fields for documenting the date, time, location, and details of the incident. It also includes sections for witness statements and a summary of any security measures taken.
Conclusion
Accurate and complete incident reporting is crucial for identifying potential hazards and preventing future incidents. By using the samples of incident report templates provided in this article, you can ensure that your incident reports are comprehensive and informative. Remember, incident reporting is an ongoing process, and it’s essential to report incidents promptly to ensure the safety of your employees and the protection of company property.
Additionally, it’s important to ensure that all incident reports are kept confidential and only shared with relevant parties, such as management, HR, or insurance companies. Maintaining confidentiality not only protects the privacy of those involved but also ensures that the information is not misused or mishandled.
In conclusion, incident reports are an important aspect of any organization’s risk management process. By documenting incidents accurately and completely, organizations can identify potential hazards, prevent future incidents, and ensure the safety of their employees and company property. With the samples of incident report templates provided in this article, you can simplify the incident reporting process and ensure that your reports are professional, informative, and effective. Remember, timely and accurate incident reporting is the key to maintaining a safe and secure workplace environment.