Learn how to write a comprehensive security incident report by examining an example. This guide will provide you with all the necessary information to write a professional report.
When a security incident occurs, it’s crucial to document it in a comprehensive report. This report serves as evidence, helps identify potential risks, and assists in creating a plan to prevent future incidents. Writing a security incident report can be challenging, but by examining an example, you can learn how to write a comprehensive report.
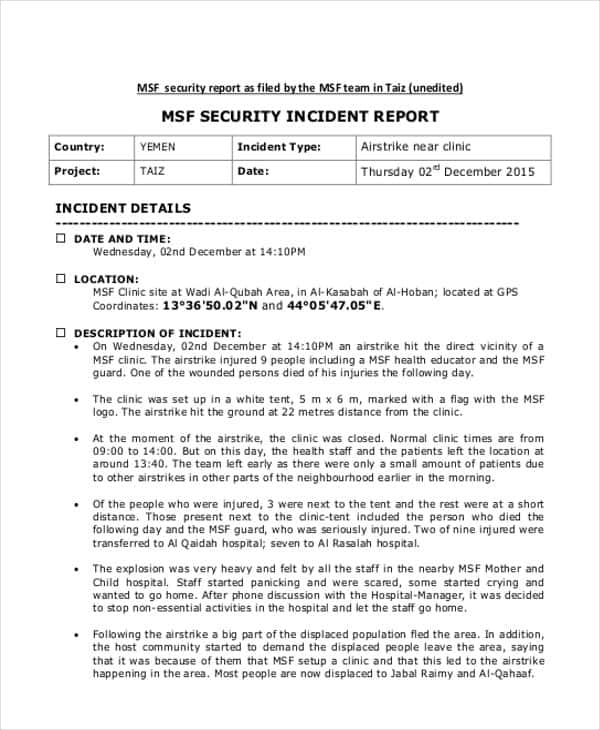
Here’s an example of a security incident report and a guide on how to write one.
- Introduction
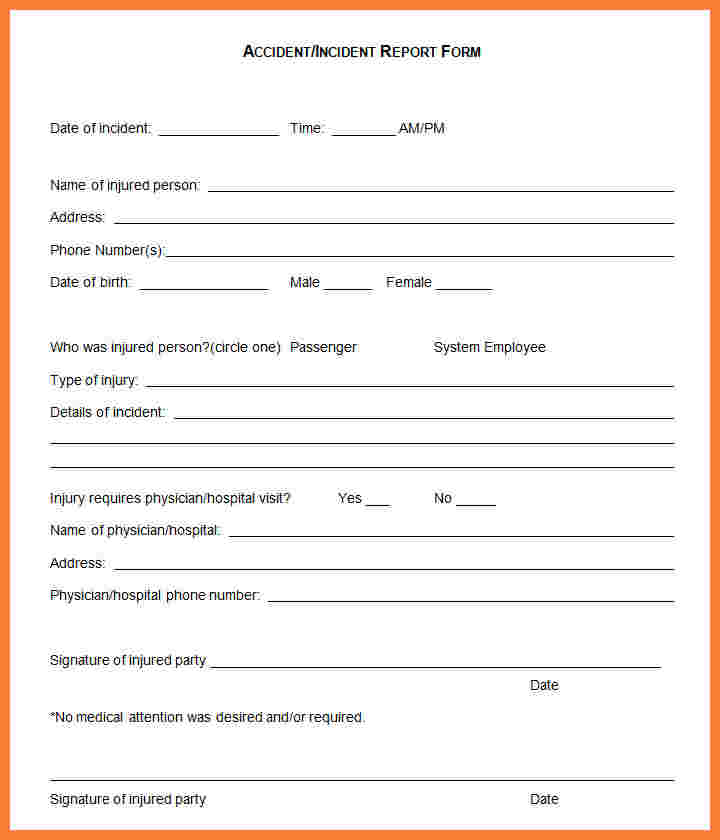
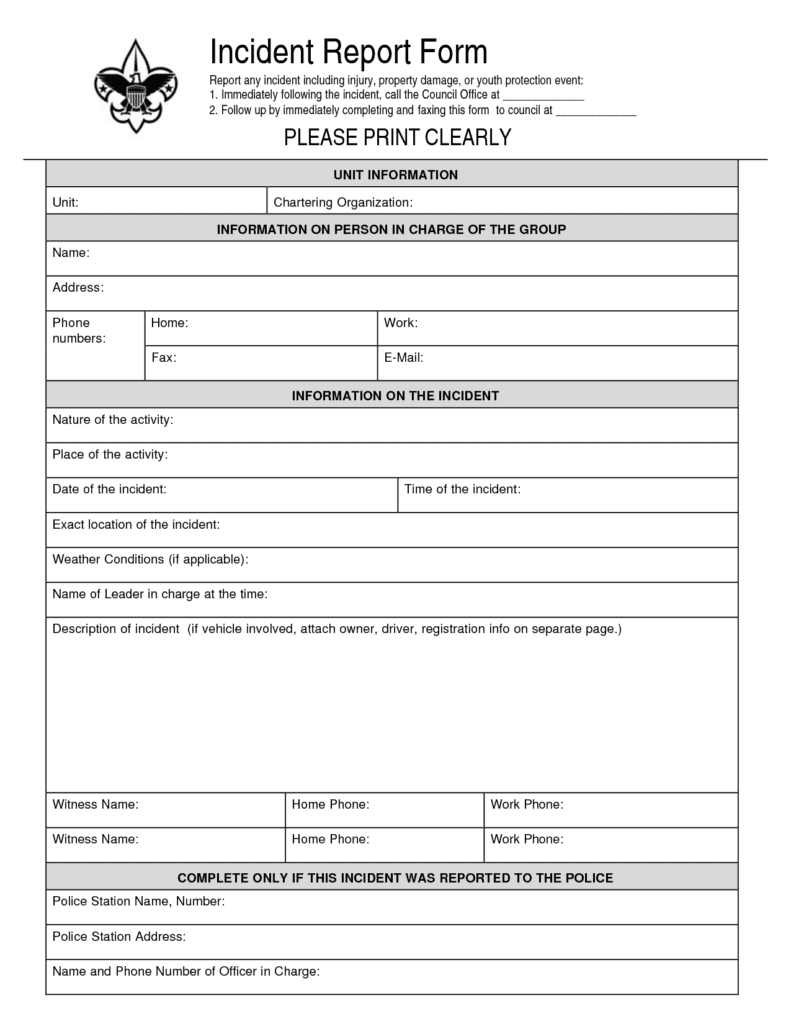
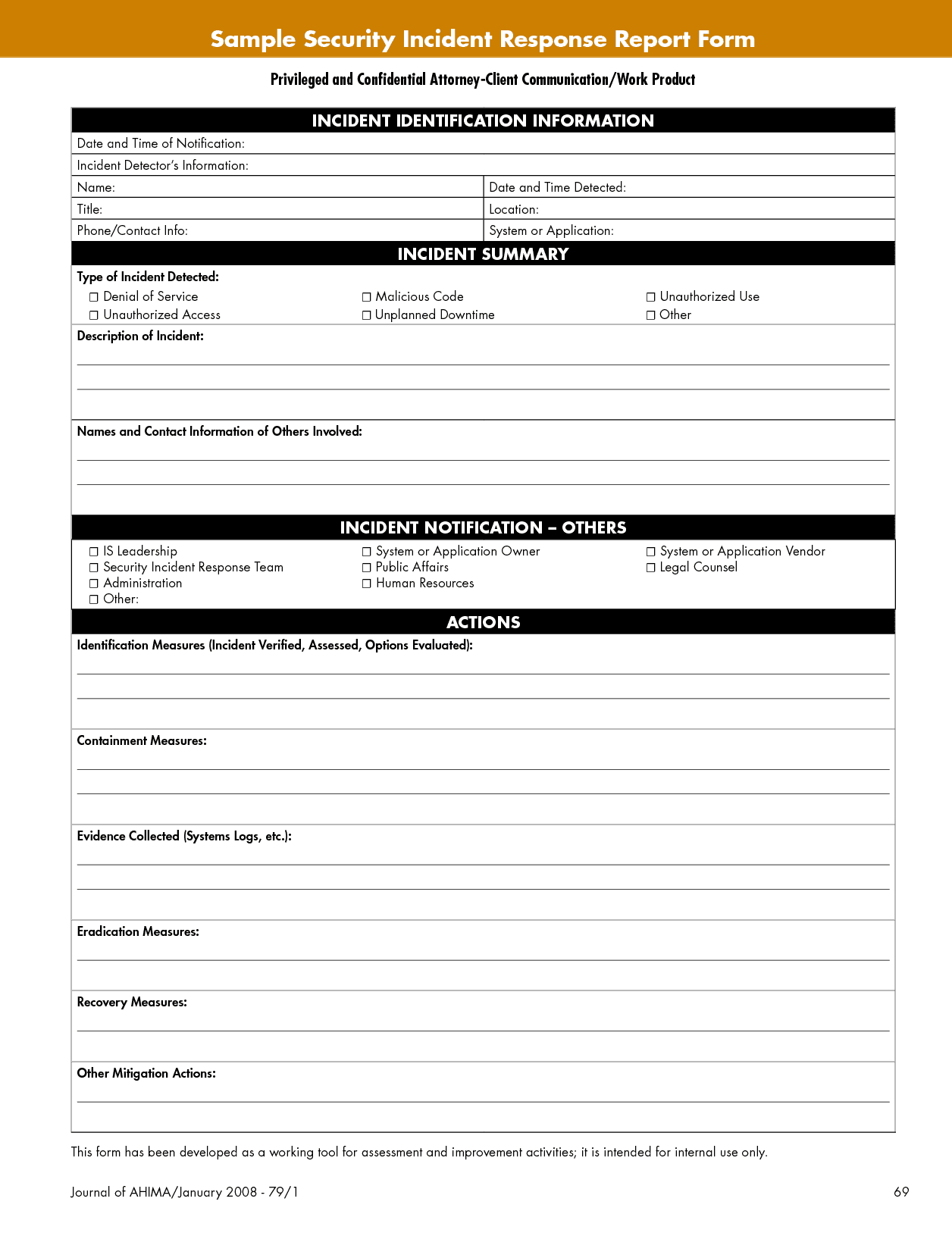
The introduction should contain general information about the incident. Include the date, time, and location of the incident. It’s also essential to include the names of the people involved. - Description of the Incident
The description of the incident should be concise and factual. Use bullet points to break down the events leading up to the incident, the incident itself, and the aftermath. Be sure to include details such as the type of incident, the severity, and any injuries or damages. - Witnesses
If there were any witnesses to the incident, their names and contact information should be included in the report. It’s essential to document their statements accurately, as they can provide valuable information about the incident. - Photos and Videos
If there are any photos or videos of the incident, they should be included in the report. Photos and videos can provide evidence and help reconstruct the events leading up to the incident. - Conclusion
In the conclusion, summarize the incident and its consequences. It’s essential to include any recommendations for preventing similar incidents from occurring in the future. - Recommendations
The recommendations section is where you can suggest measures to prevent similar incidents from occurring in the future. Include any corrective actions taken after the incident and any follow-up measures to ensure the problem is resolved. - Signatures
The final part of the security incident report is the signature section. This section should include the names and signatures of the people involved in the incident, including witnesses and the person who wrote the report. The date of the signature should also be included.
Tips for Writing a Professional Security Incident Report Writing a security incident report requires attention to detail and an understanding of the situation. Here are some tips to help you write a professional security incident report:
- Be objective
Stick to the facts and avoid any personal opinions or feelings. - Use clear and concise language
Keep the language simple and avoid using jargon or technical terms. - Use headings and bullet points
Breaking down the report into sections makes it easier to read and understand. - Be thorough
Include all relevant information and ensure the report is comprehensive. - Use active voice
Using active voice makes the report more engaging and easier to read.
Conclusion Writing a security incident report is essential in ensuring that all necessary information is documented and preserved for future reference. By examining an example report and following the tips provided, you can write a professional and comprehensive security incident report. Remember to be objective, thorough, and use clear language. A well-written report can help prevent future incidents and keep everyone safe.